Current Description
A vulnerability in the interprocess communication (IPC) channel of Cisco AnyConnect Secure Mobility Client for Windows could allow an authenticated, local attacker to perform a DLL hijacking attack on an affected device if the VPN Posture (HostScan) Module is installed on the AnyConnect client. This vulnerability is due to insufficient validation of resources that are loaded by the application at run time. An attacker could exploit this vulnerability by sending a crafted IPC message to the AnyConnect process. A successful exploit could allow the attacker to execute arbitrary code on the affected machine with SYSTEM privileges. To exploit this vulnerability, the attacker needs valid credentials on the Windows system.
Analysis Description
Download AnyConnect. Double click on the Cisco AnyConnect software icon. (If using Windows 8/8.1, from the Start screen, tap or click the Desktop tile, then tap or click the Libraries icon in the Navigation pane. Tap or click Downloads, then double-click on the Cisco AnyConnect software icon.) Click on Next on the Welcome screen. The Internet edge design covers RAVPN for laptops running the Cisco AnyConnect Secure Mobility Solution client (for SSL VPN or IP Security IPsec connections). A feature built into the Cisco AnyConnect 3.1 client is the cloud connector for Cisco Cloud Web Security (CWS) service, formerly known as Cisco ScanSafe Cloud Web Security.
A vulnerability in the interprocess communication (IPC) channel of Cisco AnyConnect Secure Mobility Client for Windows could allow an authenticated, local attacker to perform a DLL hijacking attack on an affected device if the VPN Posture (HostScan) Module is installed on the AnyConnect client. This vulnerability is due to insufficient validation of resources that are loaded by the application at run time. An attacker could exploit this vulnerability by sending a crafted IPC message to the AnyConnect process. A successful exploit could allow the attacker to execute arbitrary code on the affected machine with SYSTEM privileges. To exploit this vulnerability, the attacker needs valid credentials on the Windows system.
Severity
CVSS 3.x Severity and Metrics: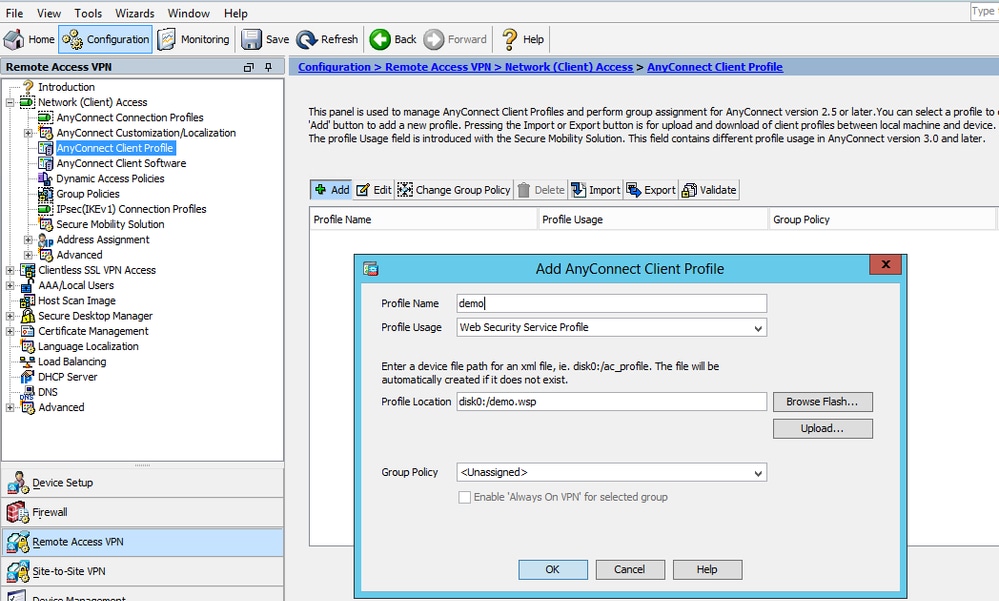
Weakness Enumeration
| CWE-ID | CWE Name | Source |
|---|---|---|
| CWE-347 | Improper Verification of Cryptographic Signature | Cisco Systems, Inc. |
Known Affected Software Configurations Switch to CPE 2.2
Denotes Vulnerable Software
Are we missing a CPE here? Please let us know.
Removing Cisco WebSecurity Addon - Cisco Community
Change History
1 change records found show changes